Microsoft Defender for Endpoint
Connect Furl to Microsoft Defender for Endpoint using Microsoft Graph API with OAuth2 authentication for vulnerability management and device inventory.
Required Licenses
Your organization must have one of the following Microsoft licenses for each capability:
For Vulnerabilities:
- Microsoft Defender for Endpoint Plan 1
- Microsoft Defender for Endpoint Plan 2
- Microsoft Defender Vulnerability Management
- Microsoft Defender XDR
For Assets/Devices:
- Microsoft Defender for Endpoint Plan 1
- Microsoft Defender for Endpoint Plan 2
- Microsoft Defender for Business
Description
Section titled “Description”Microsoft Defender for Endpoint is a unified endpoint security platform that provides advanced threat protection, vulnerability management, and security posture assessment for Windows, macOS, Linux, Android, and iOS devices. Furl integrates with Microsoft Defender for Endpoint to import device inventory and vulnerability data for comprehensive security risk management.
Configuration Steps
Section titled “Configuration Steps”-
Create an Entra App
- Log in to the Azure Portal
- Navigate to Azure Active Directory > App registrations
- Click “New registration” and create a new application
- Note the Application (client) ID and Directory (tenant) ID
-
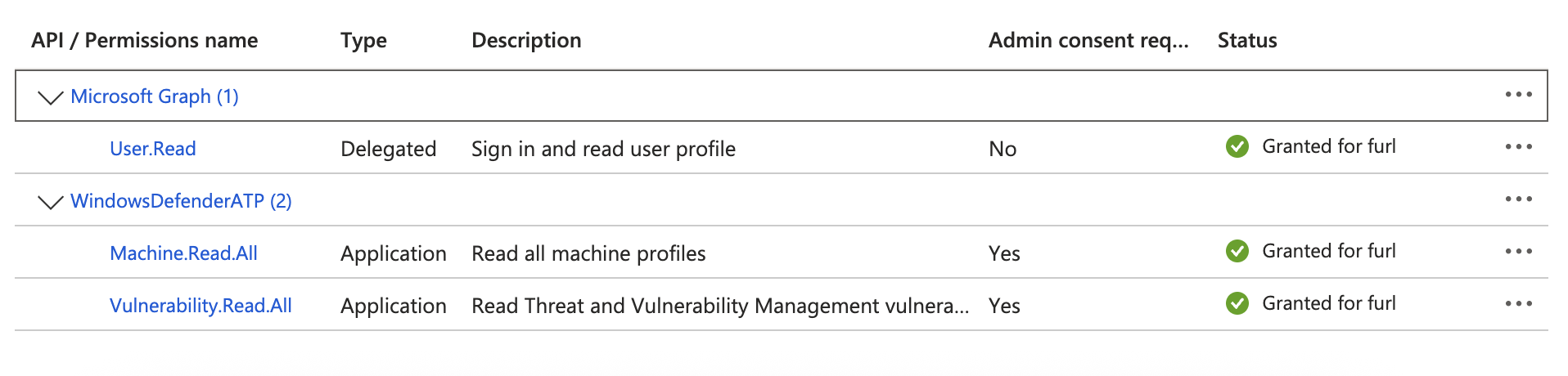
Add API Permissions
- In your app registration, go to API permissions
- Click “Add a permission” and select “APIs my organization uses”
- Search for “WindowsDefenderATP” and select it
- Select “Application permissions”
- Add the following permissions:
Machine.Read.All(for reading device/asset data)Vulnerability.Read.All(for vulnerability data)
- Click “Grant admin consent” to approve the permissions
- Create Client Secret
- Go to Certificates & secrets in your app registration
- Click “New client secret”
- Add a description and set expiration (recommend 12-24 months)
- Copy the secret value immediately (it won’t be shown again)
Required Configuration
Section titled “Required Configuration”Provide the following in Furl:
- Tenant ID - Your Microsoft Azure AD Tenant ID (Directory ID)
- Application ID - Your Azure AD Application ID (Client ID)
- Client Secret - Your Azure AD Application Client Secret
Datasource Configuration
Section titled “Datasource Configuration”Devices and Vulnerabilities
Section titled “Devices and Vulnerabilities”The Devices and Vulnerabilities datasource supports the following optional configurations:
- Device Filter - Filter devices by specific criteria using OData query syntax. Examples:
deviceName eq 'DESKTOP-ABC123'- Filter by specific device nameosPlatform eq 'MacOs'- Filter by operating system platformmachineTags/any(t: t eq 'test')- Filter by machine tags
- Vulnerability Filter - Filter vulnerabilities by severity using OData query syntax. Examples:
severity eq 'Critical'- Filter for critical vulnerabilities onlyseverity eq 'High'- Filter for high severity vulnerabilitiesseverity eq 'Critical' or severity eq 'High'- Filter for critical or high severity
Supported Capabilities
Section titled “Supported Capabilities”Datasources
Section titled “Datasources”- Devices and Vulnerabilities → Import device inventory, vulnerability findings, and associated evidence from Microsoft Defender for Endpoint to understand your security posture and prioritize remediation efforts
Actions
Section titled “Actions”Currently no actions are supported for this integration.
Troubleshooting
Section titled “Troubleshooting”- Ensure your Entra app has the correct API permissions (
Machine.Read.AllandVulnerability.Read.All) - Verify admin consent has been granted for the API permissions
- Check that your organization has the required Microsoft Defender licenses
- Ensure the client secret hasn’t expired
- Verify the Tenant ID and Application ID are correct
Additional Resources
Section titled “Additional Resources”- List machines API Documentation - Retrieve device inventory and machine information
- Export software vulnerabilities assessment API Documentation - Retrieve vulnerability data per device
- Entra App Registration Guide